Securing Mobile Apps: A 2025 Guide to Implementing Advanced Multi-Factor Authentication
In the rapidly evolving digital landscape of 2025, mobile applications are at the core of our daily lives, from banking and healthcare to communication and entertainment. This pervasive presence, however, makes them prime targets for cyberattacks. As developers and security professionals, you face the critical challenge of protecting sensitive user data and maintaining trust in an environment riddled with sophisticated threats. Traditional password-only authentication is no longer sufficient; it's a security relic waiting to be exploited.
This guide will walk you through implementing advanced Multi-Factor Authentication (MFA) strategies for your iOS, Android, and cross-platform mobile apps. We'll explore the cutting-edge techniques and best practices to fortify your applications against the ever-growing wave of cyber threats, ensuring your users' data remains secure and their experience seamless. Get ready to future-proof your mobile app security.
The Evolving Threat Landscape for Mobile Apps in 2025
The mobile threat landscape is more complex and aggressive than ever before. Attackers are constantly refining their tactics, moving beyond simple brute-force attacks to employ sophisticated phishing campaigns, credential stuffing, and malware designed specifically for mobile platforms. Your users are often the weakest link, susceptible to social engineering that compromises their login credentials.
According to recent cybersecurity reports, mobile-specific malware saw a significant surge in the past year, with an estimated 20% increase in unique variants. Furthermore, over 80% of data breaches involve compromised credentials, highlighting the urgent need for stronger authentication mechanisms. Relying solely on a username and password leaves your application and its users highly vulnerable to these persistent threats.
Actionable Takeaway: Regularly audit your application's attack surface. Understand common mobile vulnerabilities like insecure data storage, broken cryptography, and insecure communication to pinpoint where advanced MFA can offer the most significant impact.
Beyond Basic MFA: What's New and Necessary in 2025?
While SMS-based One-Time Passwords (OTPs) were once considered an improvement, they are now increasingly vulnerable to SIM-swapping attacks and interception. In 2025, advanced MFA moves beyond these easily compromised methods, focusing on stronger, phishing-resistant, and user-friendly alternatives. Here’s what you need to consider:
Biometric Authentication (FIDO Standards)
Biometrics like Face ID, Touch ID, and Android BiometricPrompt offer an excellent balance of security and convenience. Leveraging FIDO (Fast Identity Online) standards, these methods utilize secure enclaves on devices to store and process biometric data, ensuring that the user's unique identifiers never leave the device. This makes them highly resistant to remote attacks.
- iOS: Utilize
LocalAuthentication.frameworkfor Face ID and Touch ID, integrating with Keychain for secure credential storage. - Android: Implement
BiometricPromptfor a unified biometric authentication experience across devices, ensuring compatibility with various sensors.
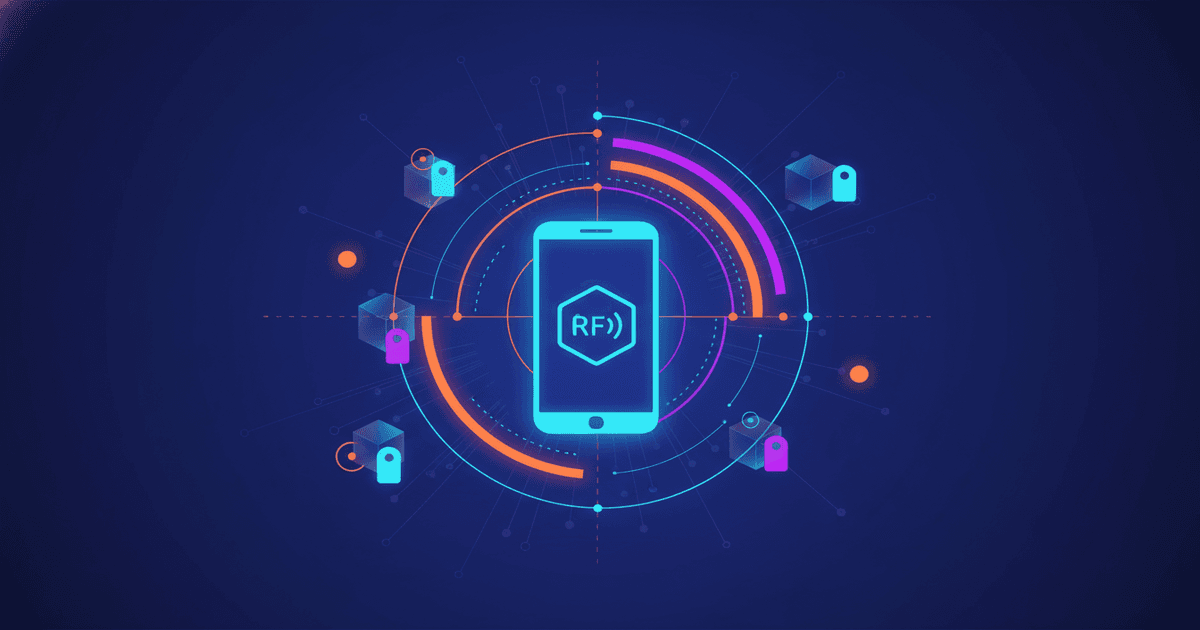
Hardware Security Keys (FIDO2/WebAuthn)
Hardware security keys, such as YubiKeys, offer the gold standard in phishing resistance. Using the FIDO2 and WebAuthn standards, these physical devices provide cryptographic proof of identity. They are immune to remote phishing attacks because the authentication secret never leaves the device and is tied to the origin of the request.
Integrating WebAuthn into your mobile apps allows users to leverage these keys via NFC, USB-C, or Bluetooth. This is especially crucial for high-value accounts or administrative access within your application ecosystem.
Behavioral Biometrics and Contextual MFA
Passive authentication methods, such as behavioral biometrics, analyze unique user patterns like typing rhythm, swipe gestures, and device handling to continuously verify identity without explicit user interaction. This adds a powerful, invisible layer of security.
Contextual MFA takes this further by incorporating factors like:
- Location-based: Restricting access or requiring stronger MFA based on geographical location (e.g., only from known corporate networks).
- Time-based: Enforcing stricter authentication during unusual login times.
- Device Attestation: Verifying the integrity of the mobile device itself (e.g., checking for root/jailbreak, detecting suspicious apps). This ensures the device hasn't been compromised before authentication even begins.
Actionable Takeaway: Diversify your MFA options. Implement a combination of biometrics, hardware keys, and contextual factors. Prioritize phishing-resistant methods for maximum protection.
Designing and Implementing Advanced MFA in Practice
Implementing advanced MFA requires careful planning and execution, focusing on both security and user experience. A clunky authentication process will lead to user frustration and potential workarounds, undermining your security efforts.
User Experience (UX) First
- Seamless Onboarding: Guide users through MFA setup with clear, concise instructions. Offer multiple MFA options and allow them to choose their preferred method.
- Intelligent Prompts: Only prompt for additional factors when necessary (e.g., new device, unusual location, high-risk transaction) using adaptive authentication logic.
- Robust Recovery: Provide secure and user-friendly account recovery options that don't rely on easily compromised methods. Consider verifiable identity checks or designated recovery codes.
Technical Integration Challenges and Solutions
1. Native iOS and Android Integration:
Leverage platform-specific APIs. For biometrics, use LocalAuthentication on iOS and BiometricPrompt on Android. For FIDO2/WebAuthn, both platforms offer robust SDKs or browser-based integration points. Securely store authentication tokens using iOS Keychain and Android Keystore, which are hardware-backed and designed for sensitive data.
// iOS Biometric Authentication Example
import LocalAuthentication
func authenticateWithBiometrics() {
let context = LAContext()
var error: NSError?
if context.canEvaluatePolicy(.deviceOwnerAuthenticationWithBiometrics, error: &error) {
context.evaluatePolicy(.deviceOwnerAuthenticationWithBiometrics, localizedReason: "Authenticate to access your account") { success, authenticationError in
DispatchQueue.main.async {
if success {
// Biometric authentication successful
} else {
// Handle authentication error
}
}
}
} else {
// Biometrics not available or not enrolled
}
}
2. Cross-Platform Frameworks (React Native, Flutter, Xamarin):
These frameworks often have community-driven or official plugins that wrap native APIs. For example, React Native's react-native-biometrics or Flutter's local_auth plugin can abstract the native biometric calls. For WebAuthn, you can often leverage webviews or platform-specific modules to bridge the functionality.
3. Backend and Identity Provider (IdP) Integration:
Utilize robust identity providers like Auth0, Okta, or Firebase Authentication. These services simplify MFA implementation, handling the complex backend logic, secure token management, and various authentication factors. Ensure your backend APIs are designed for secure token exchange and validation after successful MFA.
Actionable Takeaway: Choose an identity provider that supports advanced MFA options. Design your app's flow to prioritize user experience while maintaining strong security. Always store sensitive data, including authentication tokens, in hardware-backed secure storage.
Real-World Scenarios and Best Practices
Let's consider a scenario: a financial mobile app. For routine logins, a user might use Face ID. However, if they attempt a large fund transfer from a new device in an unusual location, the app could trigger a step-up authentication, requiring a FIDO2 security key. This adaptive approach significantly reduces fraud risk.
Phishing Resistance
Advanced MFA methods like FIDO2/WebAuthn are inherently phishing-resistant because they verify the origin of the login request. Even if a user falls for a phishing site, their hardware key will refuse to authenticate to the fake domain, effectively blocking the attack. Educate your users on why these methods are superior.
Account Recovery Strategies
No MFA strategy is foolproof without a secure account recovery process. Avoid relying on email or SMS for recovery, as these can be compromised. Instead, implement methods like:
- Recovery Codes: One-time use codes generated during setup, stored securely by the user.
- Trusted Device Recovery: Allowing recovery from a previously verified device.
- Identity Verification: Requiring government-issued ID verification for high-risk recovery scenarios.
Actionable Takeaway: Implement a multi-layered account recovery strategy. Prioritize phishing-resistant MFA for critical transactions and user actions. Continuously educate users about the importance and benefits of advanced MFA.
The Road Ahead: Future-Proofing Your Mobile MFA Strategy
The landscape of mobile security is ever-changing. To future-proof your MFA strategy, you must stay abreast of emerging technologies and threats.
- Passwordless Authentication: The trend towards truly passwordless experiences, primarily driven by WebAuthn, will continue to grow. Designing your systems to be adaptable to this paradigm shift is crucial.
- AI and Machine Learning: AI and ML will play an increasingly significant role in adaptive MFA, analyzing behavioral patterns and threat intelligence in real-time to make intelligent authentication decisions without burdening the user.
- Quantum-Resistant Cryptography: While still in its early stages, keeping an eye on quantum-resistant cryptographic standards is wise, as they will eventually impact secure communication and authentication protocols.
- Regulatory Compliance: Data privacy regulations like GDPR, CCPA, and HIPAA continue to evolve. Ensure your MFA implementation aligns with these requirements, especially concerning biometric data handling and user consent.
Conclusion
Securing mobile applications in 2025 demands a proactive and multi-layered approach to authentication. Moving beyond basic passwords and SMS OTPs to embrace advanced MFA techniques like FIDO2 biometrics, hardware security keys, and contextual authentication is no longer optional—it's imperative. By prioritizing user experience, leveraging robust identity providers, and continuously adapting to new threats, you can build mobile apps that are both secure and user-friendly.
The time to act is now. Start evaluating and integrating these advanced Multi-Factor Authentication strategies into your mobile development roadmap. Protect your users, safeguard your data, and build trust in your applications for years to come.